Recently, we realized a real demand from two customers. For security reasons, the customers required SSDs to be host-specific, which meant that SSDs could only be used locally, that when an SSD was inserted into an invalid host, the destruction process was automatically initiated, and that the host had to be able to use any non-custom SSDs from any other companies.
▶ Project Requirement Description
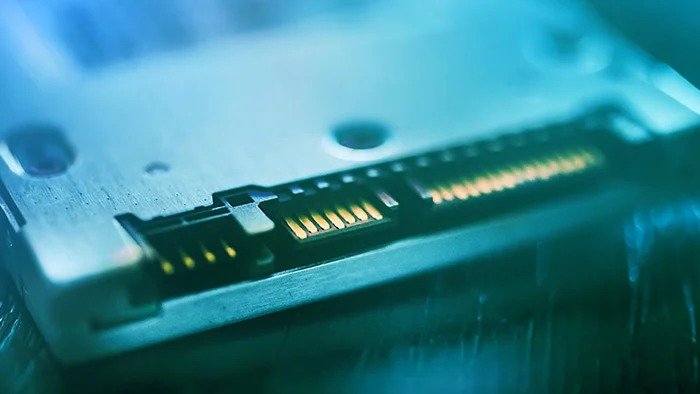
1) Host interface: SATA 6Gbps
2) Size: 2.5″
3) Capacity: 4TB
4) Storage medium: MLC
5) Ambient temperature: -40°C ~ +85°C
6) SSD can only identify a unique host;
7) When the SSD is inserted into another host, the SSD self-destruct function is enabled to destroy data.
8) The host must be able to use non-customized SSDs from other manufacturers.
▶ Overall architecture design
1) SATA 6Gb interface, 2TB capacity for single main control, using two main control group RAID0;
2) Xilinx FPGA is used as RAID0 chip, supporting Trim function;
(RAID chips on the market have the following two defects: a, can not meet industrial temperature requirements; 2. If the TRIM function is not enabled, SSD garbage collection starts only when SSD data is fully written. During garbage collection, SSD write performance deteriorates to 0MB, which may lead to invalid applications in key application scenarios.
3) Self-destruct function: Data destruction can be realized in two ways: physical burning and logical destruction (optional or all);
4) The logical destruction function can achieve rapid destruction within 10 seconds. After the destruction, The SSD can continue to be used after the “initialization” operation (all data is lost) or the SSD cannot be used any longer and must be returned to the factory for repair, but all data cannot be recovered.
5) Physical burn means that after SSD is inserted into an illegal host, all memory chips are broken down by high voltage one by one, all storage media are physically damaged, and data cannot be recovered by any means.
▶ The detailed description of function implementation
Host & SSD unique correspondence implementation
The client host SATA pin definition is not changed to ensure that other common SSDS can work properly after insertion.
An FPGA chip (or single-chip microcomputer) is added to the hard disk to realize the handshake communication between the hard disk and the main board by using SATA spare PIN. If the handshake fails within 3 seconds (time can be set freely), the data destruction function will be triggered.
For ordinary hard disks, because the spare pin is not defined, it will not shake hands with the mainboard feature code and can be used normally.
Realization and result of one-key self-destruct destruction
Safe deletion is carried out by THE GPIO action of THE IO extension chip and transmitted to the master chip. The signal pull-down for 3 seconds safe removal function is triggered, either by hardware or software. The controller sends the erase command to flash memory to initiate safe delete.
DiskMFR can destroy hard disks in two ways: logical and physical destruction.
a. Logical Destruction
Logical destruction deletes or overwrites data on a Solid-state disk (SSD) by software, including encryption keys, firmware, and mapping tables. Logical destruction does not damage storage media.
The requirements for quick deletion are as follows. The firmware implementation methods for each method are different:
1. After the deletion, the drive letter can still be seen in the OS, and normal read and write operations can still be performed after the formatting, but the deleted state is all 0xFF using the Winhex check. During the deletion, if the SSD receives a write command again or there is still data not written to Nand in the SDRAM, data will be written to the SSD after the deletion. If the data is checked by winHEX, the data is not all 0xFF. There are two solutions: First, before data destruction, clear the data in SDRAM to avoid the cache data being written into Nand Flash after safe deletion. Second, write protection is enabled during the destruction until the SSD is powered on for the second time. In this way, data is not written to the SSD by the write command received after the destruction. 2. After the SSD is deleted, the system cannot identify the SSD and cannot use software to view the internal data status.
b. Physical Destruction
Perform physical destruction on SSD flash particles will be completely burned through:
1. The unique design of DiskMFR ensures that all flash chips can be burned within 45 seconds, and there is no case that individual chips cannot be destroyed. 2. When the flash is burned, it completely destroys all the DIES in each particle, rather than just burning the IO interface. If only the IO interface is burned, then the data can still be read after the Die storing data is rewired by chip polishing. 3. If the power supply is removed during the destruction process and the unfinished burning continues after the power is powered on again, the burning will not be terminated.