Brief Introduction of AES
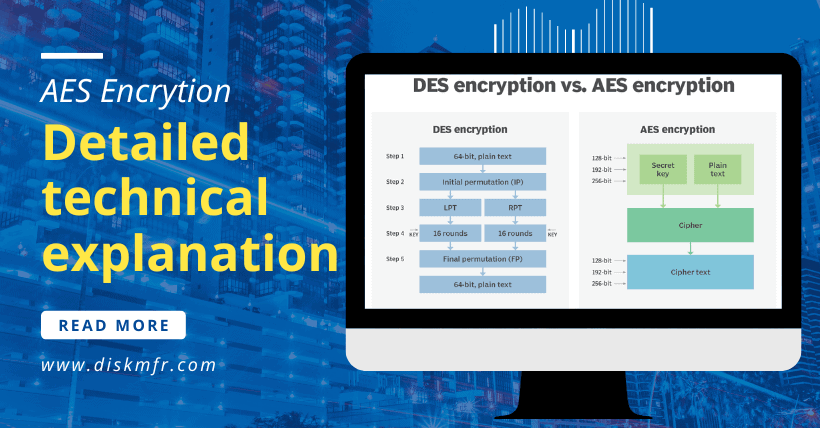
- DES is a block algorithm that uses key encryption. In 1977, it was established as the Federal Data Processing Standard (FIPS) by the US federal government’s National Bureau of Standards.
- AES Advanced Encryption Standard (AES), also known as Rijndael Encryption, is a block encryption standard adopted by the United States federal government. This standard, which replaces the original Data Encryption Standard (DES), is widely used worldwide.
1. Why is DES obsolete?
We know that the Data Encryption Standard (DES) key length is 56 bits, so the theoretical security strength of the algorithm is 2 to the power of 56. However, the mid to late 20th century is the period of rapid development of the computer. The advancement of component manufacturing technology makes the computing power of the computer more and more powerful. DES does not provide sufficient security.
In short, the DES standard secret key length requirement is too short, the security is not enough.
2. Why is the AES algorithm called the Rijndael algorithm?
On January 2, 1997, the National Institute of Standards and Technology (NIST) announced that it would propose an Advanced Encryption Standard (AES) [3] to replace DES. Many cryptographers around the world have responded to AES. world and many people have submitted their own algorithms. Five candidates made it to the final round: Rijndael, Serpent, Twofish, RC6, and MARS, with five of the authors pictured below. Finally, the Rijndael algorithm wins after rigorous steps such as security analysis, and hardware, and software performance evaluation.
3. Why AES is more secure?
The block length of AES is fixed at 128 bits and the key length can be 128 bits, 192 bits, or 256 bits. Converted into bytes, the password must be 16 bytes, 24 bytes, or 32 bytes. The longer the AES password length, the harder it is to crack, making it more secure.
symmetrical encryption
- Symmetric encryption: that is, the encryption key and the decryption key are the same.
- Asymmetric encryption: that is, the encryption key and the encryption key are not the same.
AES is a symmetric encryption algorithm with the following advantages: high encryption speed; Disadvantages: If the secret key is lost, the ciphertext is easy to crack and the security is relatively low.
RSA is an asymmetric encryption algorithm with the following advantages: security; Cons: slow encryption
AES encryption requires: plaintext + key + offset (IV) + password mode (algorithm/mode/padding)
AES decryption requires: ciphertext + key + offset (IV) + password mode (algorithm/mode/padding)
The algorithm mode of AES is usually AES/CBC/PKCS5Padding
encryption mode of AES
The AES encryption modes are as follows:
- Codebook Mode (ECB)
- Cryptographic Block Link Mode (CBC)
- Calculator Mode (CTR)
- Password Feedback Mode (CFB)
- Output Feedback Mode (OFB)
Cipher Block Link (CBC) mode: All plaintext is cut into several small segments, and each segment is XORed with the original block or ciphertext segment of the previous segment and then encrypted with the key.
Electronic Code Book (ECB): The message to be encrypted is divided into multiple blocks based on the block password block size, and each block is encrypted independently.

fill pattern of AES
For example Electronic Codebook (ECB) and Ciphertext Block Binding (CBC). The block cipher working mode, developed for symmetric key encryption, requires the input plaintext length to be an integer multiple of the block length, so the information must be filled in to meet the requirements.
1. Common Fill Pattern
| Algorithm/Pattern/Fill | 16 bytes Indicates the length of the encrypted data | The value is less than 16 bytes |
| AES/CBC/NoPadding | 16 | Nonsupport |
| AES/CBC/PKCS5Padding | 32 | 16 |
| AES/CBC/ISO10126Padding | 32 | 16 |
| AES/CFB/NoPadding | 16 | Original Data Length |
| AES/CFB/PKCS5Padding | 32 | 16 |
| AES/CFB/ISO10126Padding | 32 | 16 |
| AES/ECB/NoPadding | 16 | Nonsupport |
| AES/ECB/PKCS5Padding | 32 | 16 |
| AES/ECB/ISO10126Padding | 32 | 16 |
| AES/OFB/NoPadding | 16 | Nonsupport |
| AES/OFB/PKCS5Padding | 32 | 16 |
| AES/OFB/ISO10126Padding | 32 | 16 |
| AES/PCBC/NoPadding | 16 | Nonsupport |
| AES/PCBC/PKCS5Padding | 32 | 16 |
| AES/PCBC/ISO10126Padding | 32 | 16 |
2. So what exactly is PKCS5Padding?
Why JAVA if you specify the algorithm write AES/CBC/PKCS5Padding what each means and what it does.
- AES, encryption, and decryption algorithm
- CBC, data grouping mode
- PKCS5Padding, the data is grouped according to a certain size, and finally divided into the remaining group. If the length is not enough, it needs to be completed, which can also be called the completion mode
In short: after receiving the raw data, the data must first be clustered. If the length of the cluster does not meet the cluster conditions, it is necessary to supplement and finally form a series of clusters when using the encryption and decryption algorithm, encryption, and decryption of the multiple groups. Therefore, AES, CBC, and PKCS5Padding are indispensable in this process.
When encrypting and decrypting data, the data is usually divided into several groups according to fixed block size. Then a problem arises. If the last group is not enough for block size, what should we do? The completion process is required at this point.
Complement rules: The value of each added byte is the number of bytes that are added, i.e. N bytes, each of value N are added.
For Example:
For a 36-bit UUID, if the block size is 16 bytes (128 bits), it must be padded to 48 bits, which is a 12-byte difference. Then the last 12 filled bytes of the content are 0x0c (12) in bytes.
Offset of AES
The offset is generally added to increase AES encryption complexity and data security. The offset is normally used in AES_256, but not in AES_128 encryption.
character set
In AES encryption, special attention should also be paid to character sets. The commonly used character sets are UTF-8 and gbk.
The encryption process in action
In practice, the interaction between the client and the server is usually in the form of a string, so a good encryption process is:
- Encryption Process: Plaintext passes the key (and sometimes the offset), uses the AES encryption algorithm, then passes the Base64 transcoding, and finally outputs the encrypted string.
- Decryption Process: The encrypted string passes the key (and sometimes the offset ), uses the AES decryption algorithm, then goes through Base64 transcoding, and finally outputs the decrypted string.
The Notice of AES Encryption and Decryption
AES encryption/decryption is commonly used during communication between server and client. One end encrypts the transmission and the other end decrypts it. Although AES encryption seems simple, it can still occur during use, one end of encryption is fine but the other end of decryption fails. Once AES decryption fails, we can fix the AES problem by following aspects:
- 1. AES encryption and decryption use the same key
- 2. If the offset is involved, the offset used for AES encryption and decryption must be the same
- 3. AES encryption/decryption must use the same encryption digit, such as AES_256 ‘
- 4. AES encryption/decryption uses the same character set
- 5. AES encryption/decryption use the same encryption, filling mode, such as both using ‘AES/CBC/PKCS5Padding’ mode
- 6. Due to the influence of different development languages (such as C and Java) and different development environments (such as Java and Android), there may be differences in the implementation of the same encryption and decryption algorithm. If you notice this difference, it may lead to problems in encryption and decryption
Last but not least, when we need to verify that our AES decryption algorithm is the same as someone else’s encryption method. You can allow the encryption part to send you a ciphertext and encrypt it before the plaintext, and then use the ciphertext decryption to see if the results of the decryption and the encryption part sent you the same thing. It should be noted that the plaintext that the encryption part gave you should be as short as possible, such as the two China Characters to see whether the character set of the encryption part and the decryption part is consistent, and you can avoid copy-pasting and other links to spaces, carriage returns and other escape characters that affect the verification results.
END.